Machine Learning — Intermediate
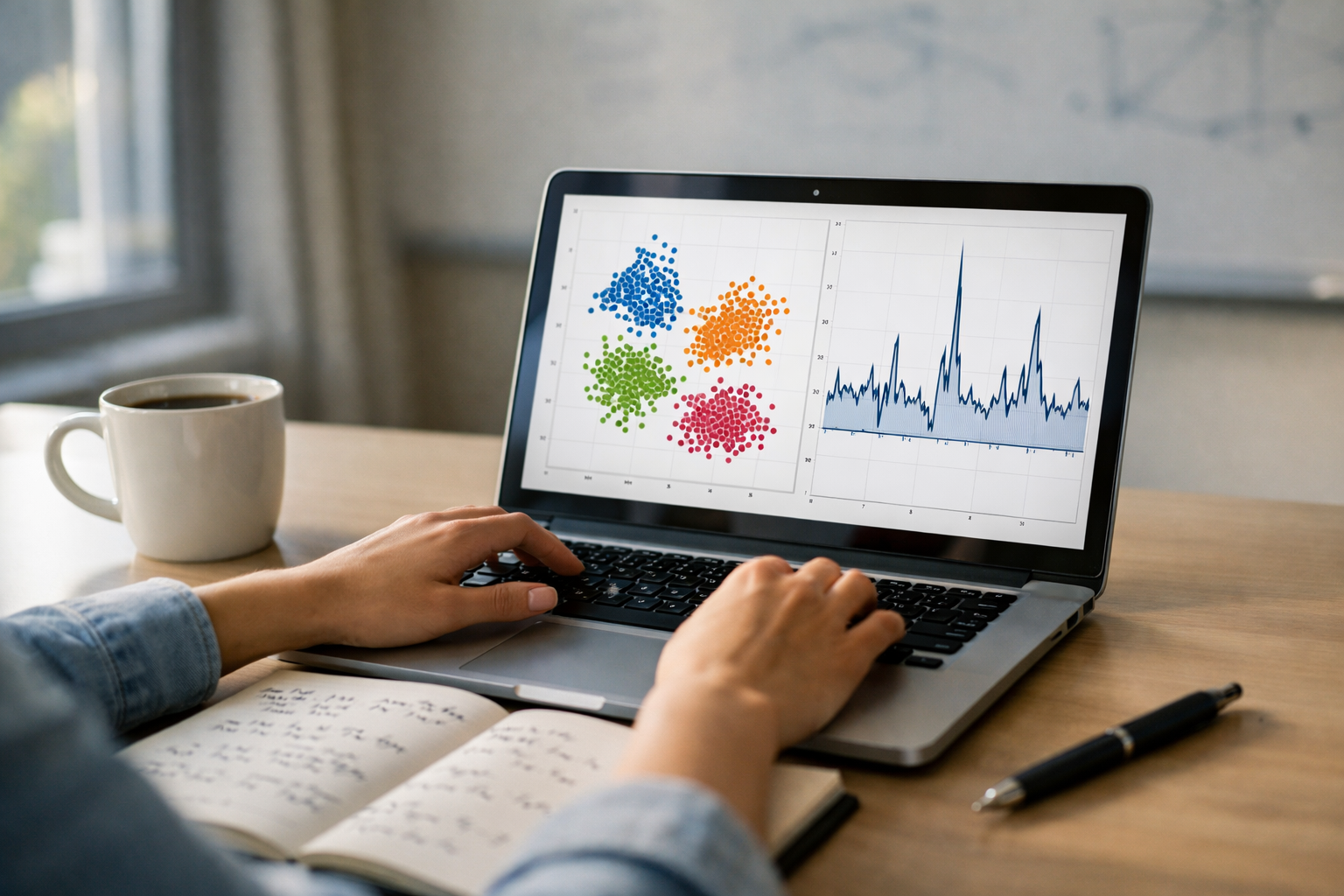
Cluster, segment, and detect anomalies with real-world unsupervised workflows.
Unsupervised learning is where many real ML projects start: you have plenty of data but few (or zero) labels. This course-book teaches you how to move from vague “let’s cluster the users” ideas to repeatable workflows that produce trustworthy segments and reliable anomaly alerts. You’ll learn how similarity, density, and data geometry shape outcomes—and how to avoid the most common traps like spurious clusters, unstable results, and misleading visualizations.
Across six tightly connected chapters, you’ll progress from problem framing and data preparation to algorithm selection, evaluation without labels, and operational delivery. The emphasis is on methods you can ship: k-means and mixtures for scalable grouping, hierarchical approaches for structure discovery, density-based techniques for irregular shapes, and anomaly detectors such as robust statistical baselines and Isolation Forest. You’ll also learn what to do when your “best metric” conflicts with what stakeholders need.
You’ll start by learning how to frame unsupervised problems and define success without labels. Next, you’ll build the data foundation—feature engineering and dimensionality reduction—so that any downstream model has a chance to work. Then you’ll implement the most common clustering families and learn when each is appropriate. After that, you’ll evaluate your clusters with metrics and stability checks and learn how to communicate results with credible evidence. With that foundation, you’ll build anomaly detection systems and choose thresholds that match operational reality. Finally, you’ll deliver segmentation as a product: turning clusters into decisions, monitoring for drift, and packaging an end-to-end blueprint.
This course is designed for learners who already know basic Python and introductory ML concepts and want to become effective at real-world unsupervised learning. If you’ve tried clustering before and weren’t sure whether the results were “good,” this course gives you a repeatable way to decide.
If you’re ready to build unsupervised learning systems you can defend and deploy, Register free to begin. Prefer to compare options first? You can also browse all courses on Edu AI.
Senior Machine Learning Engineer (Applied Unsupervised Systems)
Sofia Chen is a Senior Machine Learning Engineer focused on unsupervised and weakly supervised systems for monitoring, personalization, and risk. She has shipped clustering and anomaly detection pipelines across consumer and B2B products and mentors teams on evaluation, drift, and deployment best practices.
Unsupervised learning is what you reach for when you have plenty of data but no reliable labels. That’s common in real organizations: you may have millions of transactions, clicks, support tickets, sensor readings, or customer profiles, yet no agreed-upon “ground truth” for what the groups are or which events are “bad.” The promise is discovery: let patterns in the data guide you toward structure you can use. The risk is equally real: without labels, it’s easy to over-interpret noise or optimize a metric that doesn’t reflect business value.
This chapter builds the mental model you’ll use throughout the course: (1) identify whether your problem is clustering, anomaly detection, or segmentation; (2) translate the business question into an unsupervised objective; (3) establish a minimal exploratory baseline and sanity checks; and (4) choose success criteria without labels, using proxies and guardrails. You will learn to make engineering judgments that keep unsupervised projects grounded: what signal you expect, how similarity should be defined, what “good” looks like operationally, and how to know when results are unstable or misleading.
A practical framing: unsupervised learning rarely “answers” a business question by itself. It produces candidate structure (clusters, neighborhoods, outliers) that you must validate against reality: domain knowledge, downstream outcomes, operational constraints, and stakeholder review. Your goal is not perfect truth; it is useful, repeatable structure that helps people make better decisions.
Practice note for Identify clustering vs anomaly detection vs segmentation use cases: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Translate a business question into an unsupervised objective: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Build a minimal exploratory baseline and sanity checks: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Choose success criteria without labels (proxies and guardrails): document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Identify clustering vs anomaly detection vs segmentation use cases: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Translate a business question into an unsupervised objective: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Build a minimal exploratory baseline and sanity checks: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Choose success criteria without labels (proxies and guardrails): document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Identify clustering vs anomaly detection vs segmentation use cases: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Unsupervised learning shows up in three recurring roles: discovery, compression, and monitoring. Discovery is about finding natural groupings or themes—e.g., “What kinds of usage behaviors exist?” That’s classic clustering, often used as a first pass to generate hypotheses. Compression is about representing data more simply—e.g., mapping high-dimensional behavior into a few coordinates (dimensionality reduction) or a handful of discrete groups. Compression supports reporting, visualization, and downstream models.
Monitoring focuses on “what looks unusual,” which is anomaly detection. Here the question is not “how many groups are there?” but “what should trigger investigation?” A key lesson is to separate anomalies (rare or surprising given a baseline) from outliers (extreme values on one feature) and from novelty (new patterns that appear over time). Monitoring systems also require operational thinking: alert volumes, escalation paths, and feedback loops.
Segmentation is often discussed alongside clustering, but it is a product decision more than a modeling task. Segmentation answers “How should we categorize entities to act on them?” A clustering algorithm may propose groups, but a usable segment must be interpretable, stable, and aligned with actions (pricing, onboarding, risk controls). This is why the first step in any unsupervised project is use-case identification: are you trying to understand structure (clustering), find suspicious events (anomaly detection), or define actionable buckets (segmentation)? Confusing these leads to wasted effort—for example, running k-means on fraud events when the actual need is an alerting threshold tuned to investigation capacity.
Unsupervised methods succeed or fail based on how well your features express similarity. Before selecting an algorithm, inventory your data types and decide how “closeness” should work for the business. Numeric features (spend, latency, temperature) typically need scaling. If one feature ranges from 0–1 and another from 0–1,000, Euclidean distance will be dominated by the large-scale feature unless you standardize or use robust scaling. This is not cosmetic; it changes the geometry of your dataset and therefore the clusters you see.
Categorical features (country, plan type, device) require careful encoding. One-hot encoding can work, but it creates sparsity and can overweight rare categories. Alternatives include target-free embeddings, frequency encoding (with guardrails), or using similarity measures designed for mixed data. The key is to avoid injecting unintended meaning: for categories, numeric codes (e.g., country=1,2,3) create fake distances.
Text and logs are high-dimensional by nature. Bag-of-words or TF-IDF vectors create sparse representations where cosine similarity often makes more sense than Euclidean distance. With time series, similarity depends on what you care about: absolute level, shape, seasonality, or timing shifts. You might compare engineered summaries (mean, trend, volatility), or use sequence-aware distances. The practical workflow is to start simple: create a feature table that matches your operational unit (customer, device, transaction), then iterate. A minimal baseline might use a handful of well-understood numeric summaries plus a small set of categorical indicators, scaled consistently and checked for missingness and leakage.
Most unsupervised algorithms are easier to choose when you think in three intuitions: distance, density, and graphs. Distance-based methods (like k-means) assume clusters are roughly compact regions in the chosen feature space. They work well when “average behavior” defines a group and features are scaled appropriately. They struggle with elongated shapes, variable density, or heavy categorical/text sparsity unless preprocessing is strong.
Density-based methods (DBSCAN/HDBSCAN-style concepts) treat clusters as regions of high point concentration separated by low-density gaps, and label sparse points as noise. This intuition fits anomaly detection naturally: anomalies often live in low-density regions. Density methods can discover non-spherical shapes, but they require careful parameterization and can be sensitive to differing densities across the dataset.
Graph-based thinking connects each point to its neighbors, forming a network where communities can be found. Even if you don’t explicitly build graphs, many modern techniques behave like this under the hood (nearest-neighbor structures, connectivity in hierarchical clustering). Graph intuition is also useful for sanity checks: if tiny perturbations in features rewire neighbor relationships, your clusters may be unstable.
Translating a business question into an unsupervised objective is about choosing which intuition matches the action. Example: “Find new customer types for tailored onboarding” suggests clusters that are interpretable and stable (often distance-based with strong feature curation). “Detect compromised accounts” suggests a baseline of normal behavior plus a scoring rule for rarity (density/Isolation Forest). “Group similar incidents from tickets” may be text similarity and graph communities. The objective should be stated operationally: produce N segments with clear profiles; produce anomaly scores with a manageable alert rate; produce clusters that remain consistent month-to-month.
Unsupervised learning fails quietly: it will always return something, even when the data has no meaningful structure. One failure mode is spurious clusters driven by artifacts—missing-value patterns, duplicated records, seasonality, or a single dominant feature. Another is confounding: clusters that simply reflect “data collection differences” (region, device type, pipeline changes) rather than the behavior you intend to analyze. A third is resolution mismatch: the algorithm finds micro-clusters when you need coarse segments, or vice versa.
Instability is especially dangerous. If re-running the pipeline (with a new sample, a different seed, or the next month of data) yields very different cluster assignments, you cannot build operational processes on top of it. Your minimal exploratory baseline should include sanity checks: visualize key feature distributions per cluster, check cluster sizes (avoid many singletons unless you are doing anomaly work), and confirm that clusters are not trivially explained by one feature or by data quality flags.
Without labels, success criteria must rely on proxies and guardrails. Proxies include internal cohesion/separation metrics (silhouette, Davies–Bouldin), but do not treat them as the goal; they reward certain shapes and can be gamed by scaling choices. Add stability checks: bootstrap samples, perturb features, or train on one time window and assign on another; measure agreement (e.g., adjusted Rand index) and track drift. Guardrails are business constraints: segments must be large enough to act on, must not correlate too strongly with protected attributes without justification, and must be explainable to stakeholders. A practical rule: if you cannot explain why two points are “similar” in business terms, the distance metric is wrong or the features are unhelpful.
Unsupervised outputs can cause real harm because they often feel objective: “the data discovered these groups.” In segmentation, the main risks are stereotyping and proxy discrimination. Even if you exclude protected attributes, other features can act as proxies (location, device, language). A segment used for differential treatment (pricing, eligibility, support priority) must be reviewed for fairness and intent. Practical mitigations include documenting feature choices, auditing segment composition across sensitive groups, and restricting how segments are used (e.g., personalization vs denial of service).
Anomaly detection has a different risk profile: false alarms can overwhelm teams and erode trust, while false negatives can miss critical incidents. Because there are no labels, you must design the system around operational capacity and investigation cost. Define what happens after an alert: who investigates, what evidence they need, how feedback is recorded, and how thresholds are adjusted. Start with a conservative baseline (simple statistical rules or robust z-scores) to establish expected alert volume before deploying more complex models like Isolation Forest or density scoring.
Ethical engineering also means respecting privacy and data minimization. Feature tables for clustering can easily become “everything we have,” which increases risk without improving utility. A good practice is to articulate the minimal set of features needed to support the business objective, retain data for a justified period, and ensure segments/anomaly scores are not repurposed beyond their stated use without review.
A successful unsupervised project looks like a product workflow, not a one-off notebook. Start by defining the entity (customer, account, device, transaction) and the time window (last 30 days, rolling week). Build a dataset that is reproducible: versioned extraction logic, clear handling of missing values, and a data dictionary. Then implement a minimal baseline and sanity checks before any heavy tuning: simple feature scaling, a small k-means run, a basic hierarchical dendrogram on a sample, or a robust anomaly score on a handful of key metrics. The goal is to test whether signal exists and whether your similarity definition makes sense.
Translate the business question into an unsupervised objective and deliverables. For clustering/segmentation, deliverables typically include: (1) cluster assignments with confidence or distance-to-center, (2) profiles per cluster (top distinguishing features, representative examples), (3) names and narratives that business partners can use, and (4) stability analysis across resamples and time. For anomaly detection, deliverables include: (1) an anomaly score, (2) a thresholding policy tied to alert capacity, (3) explanations or contributing features where possible, and (4) monitoring dashboards for drift and alert rates.
Define success criteria without labels using a blend of metrics and guardrails. Metrics: internal cluster quality, stability, coverage (how many points are assigned vs labeled noise), and alert precision estimates from sampled investigations. Guardrails: segment interpretability, minimum size, fairness checks, and operational constraints. Finally, plan the iteration loop: feature refinement (scaling, encoding, sparsity handling), algorithm selection (k-means, hierarchical, DBSCAN/HDBSCAN-style), and evaluation. If you treat this as an engineering system—with baselines, checks, and clear objectives—unsupervised learning becomes a dependable tool rather than a source of pretty but unreliable plots.
1. In an organization with lots of data but no reliable labels, what is the main promise and the main risk of using unsupervised learning?
2. Which sequence best matches the chapter’s recommended workflow for keeping an unsupervised project grounded?
3. Why does the chapter say unsupervised learning rarely “answers” a business question by itself?
4. When choosing success criteria without labels, what does the chapter recommend using to judge whether results are “good”?
5. Which choice best captures the chapter’s goal for an unsupervised learning project?
Unsupervised learning looks “automatic,” but in practice it is unusually sensitive to data preparation. In supervised work, labels provide an anchor that can partially counteract messy features. In clustering and anomaly detection, your model’s entire worldview is defined by similarity—often a distance metric applied to the features you provide. If the preprocessing makes irrelevant attributes dominate the distance, the model will confidently produce clusters that are mathematically valid and business-useless.
This chapter focuses on building similarity that matches your intent: cleaning, encoding, scaling, handling missingness and outliers without leaking conclusions, reducing dimensionality for signal and interpretability, and packaging the whole process into reusable pipelines. The outcome is not “perfect data,” but a defensible, repeatable transformation from raw tables to feature spaces where distance-based methods behave sensibly.
A practical workflow is: (1) inventory feature types and leakage risks; (2) decide how to encode each type; (3) choose scaling/normalization consistent with your algorithm; (4) decide how missingness and outliers will be treated (and how you’ll measure sensitivity); (5) address high dimensionality and sparsity; (6) place everything into a pipeline so you can rerun, tune, and audit. Throughout, keep one engineering question in mind: what differences between rows should count as “similar” for the business problem?
The next sections break the chapter into concrete decisions you’ll make repeatedly—whether you’re segmenting customers, clustering documents, or flagging anomalous transactions.
Practice note for Clean, encode, and scale features for meaningful similarity: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Handle missingness and outliers without leaking conclusions: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Reduce dimensionality to improve signal and interpretability: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Package preprocessing into reusable pipelines: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Clean, encode, and scale features for meaningful similarity: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Handle missingness and outliers without leaking conclusions: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Reduce dimensionality to improve signal and interpretability: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Package preprocessing into reusable pipelines: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Start with a feature inventory. Unsupervised datasets commonly mix numeric (amounts, counts), categorical (country, plan type), ordinal (risk tier), boolean (is_active), text-derived tokens, and timestamps. Each type needs an encoding that preserves meaning without injecting artificial geometry. A frequent mistake is to treat IDs (customer_id, device_id) as numeric; distance then reflects arbitrary ID gaps rather than behavior.
One-hot encoding is the default for low-to-moderate cardinality categoricals. It makes categories equidistant and avoids imposing a false order. But one-hot explodes dimensionality and produces sparse matrices; that’s not inherently bad, but it changes which algorithms and metrics are practical. In particular, Euclidean distance on one-hot can behave unintuitively when the number of active bits differs across rows, so you may later prefer cosine distance or normalization.
When cardinality is high (thousands of categories), one-hot can be too wide. In unsupervised settings, avoid label-dependent encoders (like mean target encoding) because there is no target—and because creating pseudo-targets based on cluster assignments is circular and leaks your conclusions back into features. Prefer target-free encoders such as frequency/count encoding (replace category with its global frequency), ordinal encoding with careful handling of unknowns, or learned embeddings from separate self-supervised objectives. Frequency encoding often works well for anomaly detection: rare categories can legitimately signal unusual behavior, but verify that “rare” is not simply “newly introduced” (time leakage).
Feature hashing is a strong choice for very high-cardinality categoricals or tokenized text. It maps categories into a fixed number of columns, controlling dimensionality and memory. The trade-off is collisions: unrelated categories can share the same hashed bin. In practice, choose a sufficiently large hash space (e.g., 2^18 or 2^20) and validate that clustering stability doesn’t change dramatically when you vary the hash size. Hashing is also operationally convenient because it naturally handles unseen categories at inference time.
Finally, treat timestamps deliberately. Raw epoch time often dominates distance and turns clusters into “older vs newer.” Instead, derive cyclical and behavioral features: hour-of-day and day-of-week (sin/cos), time since last event, rolling counts, or session duration. The guiding rule: encode what you want similarity to mean, not what is easiest to compute.
For distance-based methods, scaling is not a cosmetic step; it is the model. If one feature ranges from 0–1 and another from 0–1,000, the second will dominate Euclidean distance. Before choosing a scaler, decide what “one unit of change” should mean across features. A good heuristic is to make typical variations comparable unless you explicitly want a feature to carry more weight.
Standardization (z-score) (subtract mean, divide by standard deviation) is common for k-means, Gaussian mixture models, and PCA. It assumes features are roughly symmetric and that standard deviation is a sensible scale. If a feature is heavy-tailed (e.g., revenue), standardization can still leave extreme values dominating; consider a log transform first (log1p for counts) or use robust scaling.
Min–max scaling maps features into a fixed range, often [0, 1]. It preserves relative spacing but is sensitive to outliers: a single extreme value can compress the bulk of the data into a tiny interval. Use it when bounds are meaningful (percentages, probabilities) or when you need comparability for cosine-like similarity in nonnegative spaces, but pair it with clipping/winsorization if outliers are expected.
Robust scaling (center by median, scale by IQR) is often a better default for anomaly detection or transactional data with long tails. It reduces the influence of extreme values so clusters aren’t driven by a handful of anomalies—ironically important because you may want to detect anomalies after clustering rather than have them distort the clustering itself.
Normalization (row-wise scaling to unit norm) is different from feature scaling. It makes each sample vector length 1, shifting the focus from magnitude to direction. This is beneficial for text TF-IDF vectors and other sparse high-dimensional representations where cosine similarity is appropriate. It can be harmful for numeric business features when magnitude is meaningful (e.g., total spend); normalizing would make a big spender look similar to a small spender with the same proportions.
Common mistakes: applying scaling before splitting (leakage), mixing incompatible scalers across columns without tracking them, and assuming the algorithm “handles it.” Build the scaler choice into your model selection: k-means + StandardScaler, DBSCAN + RobustScaler, cosine-based clustering + Normalizer, and always verify with stability checks (do clusters persist under reasonable scaler variations?).
Missingness is informative in real systems: customers omit optional fields, sensors drop readings, and logs fail intermittently. In unsupervised learning, naive imputation can create artificial similarity. For example, filling missing income with the mean makes all unknown-income customers look alike, potentially forming a “missingness cluster” that is more about data collection than behavior.
Start by classifying missingness patterns: sporadic vs systematic, correlated with time, geography, product versions, or user segments. Add missingness indicators (boolean “was_missing”) for features where missingness may carry signal. This often improves anomaly detection because “missing where it should exist” can be unusual. But be cautious: indicators can also dominate distance if many columns are missing for a subset, so combine with sensible scaling.
For numeric features, simple imputation is often sufficient if paired with indicators: median imputation is robust; mean imputation is fine for symmetric distributions; constant imputation (e.g., 0) is appropriate only when 0 is a legitimate neutral value. For categorical features, impute a special category such as “__MISSING__” to avoid blending missing with a real category. Avoid complex imputation (KNN imputation, iterative models) unless you can justify that it won’t leak structure you are trying to discover; sophisticated imputers can “smooth” the data and erase small clusters or anomalies.
Outliers and missingness interact. If you clip outliers and impute afterward, you may hide true anomalies; if you impute and then scale, the imputed values can influence the scale estimates. A robust order of operations is: (1) split data (or define fit scope); (2) fit imputers on the fit data; (3) apply safe transforms (log, clipping) with documented thresholds; (4) scale. For clipping, prefer quantile-based winsorization (e.g., cap at 1st/99th percentiles) fit on training data, and record the caps for reproducibility.
Most important: do not “clean based on clusters.” Removing points because they look like outliers after you run clustering is a form of conclusion leakage. Instead, define preprocessing rules from domain constraints (impossible values, known measurement errors) and run sensitivity analyses: rerun the pipeline with and without clipping, or with different imputations, and check whether the high-level cluster story remains stable.
As dimensionality grows, distance metrics become less discriminative. In high dimensions, the nearest and farthest neighbors can end up at similar distances, making “closest cluster center” an unreliable concept. This curse of dimensionality is especially acute when many features are noisy, redundant, or mostly zero (sparse). The result is clusters that are unstable, sensitive to tiny perturbations, or dominated by artifacts of scaling.
Sparsity has two faces. In one-hot or hashed features, sparsity is expected and can be helpful, but it changes which algorithms are feasible. Classic k-means expects dense vectors and Euclidean geometry; it can be inefficient and semantically weak on very sparse binary data. Alternatives include cosine-based clustering, spherical k-means (conceptually), or density methods that can work with appropriate distance measures. If you stay in scikit-learn, be mindful of which estimators accept sparse matrices and how they compute distances.
Practical steps to manage high-dimensional spaces:
A common mistake is to “throw everything in” because there is no target to overfit. Unsupervised models can still overfit—by fitting noise patterns that are stable only in your sample. Treat feature selection as risk management: every extra column is another way to create accidental similarity. The practical outcome you want is a feature space where distances reflect meaningful behavioral differences and where clusters remain similar when you resample data or slightly change preprocessing.
Dimensionality reduction serves two purposes: improve signal-to-noise for downstream clustering/anomaly models and provide interpretable views for humans. Use it deliberately, not as a default. If your raw features already align with business concepts, aggressive reduction can hide actionable drivers. If your feature space is high-dimensional and redundant, reduction can stabilize distance computations and speed up model training.
PCA is the workhorse for numeric, roughly linear structure. After standardization, PCA finds directions of maximal variance. It often helps k-means and Gaussian mixtures by removing correlated dimensions and concentrating signal. Choose the number of components via explained variance (e.g., 80–95%) or via stability: if cluster assignments are more stable across resamples after PCA, it’s doing useful work. Remember: PCA components are linear combinations; for interpretation, inspect loadings and back-map clusters to original features via profiling.
Random projections are a practical option when you need speed and approximate distance preservation. They can be surprisingly effective for large sparse matrices (text, hashed categoricals) because they reduce dimensionality with minimal tuning. The trade-off is interpretability: projected dimensions are not meaningful. Use random projections when operational constraints (memory/latency) matter more than explaining axes.
UMAP and t-SNE are primarily visualization tools. They excel at producing 2D/3D embeddings that reveal local neighborhoods, but they distort global distances. A common mistake is to cluster in t-SNE space and then present those clusters as objective segments; t-SNE can create apparent separation even when none exists. If you use UMAP for clustering, treat it as a model component: fix random seeds, tune neighbors/min_dist, and validate stability. Prefer clustering in the original (or PCA-reduced) feature space and use UMAP/t-SNE to explain clusters visually, not to define them.
Operational guidance: fit reducers only on training data, persist the fitted reducer, and ensure the same transformation is applied in production. For anomaly detection, be cautious: reduction can wash out rare-but-important signals. Always evaluate whether anomalies remain separable after reduction by checking rank stability of anomaly scores under different component counts.
Unsupervised projects fail in production less from modeling than from inconsistent preprocessing. The fix is to treat preprocessing as code, not a notebook side effect. In scikit-learn, Pipeline and ColumnTransformer let you define a single, reusable object that (a) fits all transformations on the correct data scope, (b) applies the same logic at inference, and (c) can be tuned and cross-validated consistently.
Use a ColumnTransformer to apply different transformations to different column groups: numeric (imputer + scaler), low-cardinality categoricals (imputer + one-hot), high-cardinality categoricals (imputer + hashing or frequency encoding), and optional text (TF-IDF + normalization). Then wrap it in a Pipeline with your clustering or anomaly model. This design prevents leakage because calling fit trains imputers/scalers only on the fit data, and calling transform applies fixed parameters.
Reproducibility practices are non-negotiable: set random_state for reducers and stochastic models, persist the full pipeline with versioned artifacts, and log the feature lists used by each transformer. When columns change (a common real-world event), pipelines can break silently. Guard with schema checks (expected columns, dtypes) and decide a policy for unknown categories (ignored vs hashed vs error).
Finally, pipelines make experimentation honest. You can grid-search preprocessing choices alongside model hyperparameters: StandardScaler vs RobustScaler, PCA component counts, hashing dimensions, and imputation strategies. For unsupervised evaluation, you’ll often use internal metrics (silhouette, Davies–Bouldin) and stability checks (bootstrap consistency). Those checks only mean something when the entire preprocessing+model chain is consistent. A well-structured pipeline turns clustering outputs into repeatable segments that can be profiled, named, validated with stakeholders, and re-generated on new data without drifting due to ad hoc transformations.
1. Why is data preparation especially critical for clustering and anomaly detection compared to supervised learning?
2. What does the chapter mean by saying “similarity is a design choice”?
3. Which practice best prevents subtle leakage when preprocessing for unsupervised models?
4. A clusterer is producing mathematically clean but business-useless clusters. Which is the most likely cause described in the chapter?
5. What is a key reason to package preprocessing into reusable pipelines in this chapter’s workflow?
Clustering is rarely about discovering “the one true structure” in your data. In practice, you’re building a useful partition: segments you can describe, validate, and act on, or groups that improve downstream decisions (routing, personalization, risk triage). That means algorithm choice is an engineering decision as much as a statistical one: you trade off speed vs. expressiveness, stability vs. sensitivity, and interpretability vs. flexibility.
This chapter focuses on the clustering methods that show up repeatedly in real projects—k-means, hierarchical clustering, and density-based approaches (DBSCAN-style thinking). You’ll learn how to train them, read their outputs (centroids, inertia, dendrogram cuts, noise points), and avoid common pitfalls such as clustering on unscaled features or forcing spherical clusters onto non-spherical geometry.
As you read, keep a simple workflow in mind: (1) clarify the objective (segmentation, compression, prototype discovery, or noise detection), (2) prepare features for distance calculations (scaling, encoding, sparsity handling), (3) fit multiple clustering models with reasonable hyperparameter sweeps, (4) evaluate with internal metrics and stability checks, and (5) translate clusters into narratives and operational rules. The goal is not just “clusters,” but defensible, repeatable segments.
The sections below are designed as “field notes”: what assumptions each method makes, what knobs matter, what breaks first, and what a good deliverable looks like when you’re done.
Practice note for Train k-means and interpret centroids and inertia: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Use hierarchical clustering to reveal structure and choose cuts: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Apply density-based clustering for irregular shapes and noise: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Select algorithms based on data geometry and constraints: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Train k-means and interpret centroids and inertia: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Use hierarchical clustering to reveal structure and choose cuts: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Apply density-based clustering for irregular shapes and noise: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Select algorithms based on data geometry and constraints: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
k-means is the workhorse for segmentation because it’s fast, simple to explain, and produces centroids you can treat as prototypes. Its core assumption is geometric: clusters are roughly spherical (or at least convex) in the chosen feature space, and “close” points should belong together under a distance metric—usually Euclidean. If your features are on different scales, k-means will happily cluster on the largest-scale feature (often a bug, not a feature), so standardization is not optional.
Training k-means alternates between assigning each point to the nearest centroid and recomputing centroids as the mean of assigned points. The objective it minimizes is within-cluster sum of squares (WCSS), often reported as inertia. Inertia is useful for comparing runs on the same dataset and feature representation, but it is not comparable across different scalings or feature sets.
Initialization matters because k-means optimizes a non-convex objective. Use k-means++ (or similar) and run multiple initializations (e.g., 10–50) to reduce the chance of a poor local minimum. A common mistake is reporting one run’s clustering as if it were definitive; for production work, you want either multiple restarts or a stability check (how often points stay in the same cluster across seeds).
When data is large, mini-batch k-means is the practical variant. Instead of computing updates over all rows, it updates centroids using small random batches, drastically reducing time and memory while usually preserving segment quality. Mini-batches are especially useful for high-volume logs and clickstream data where you care about speed and approximate prototypes. The trade-off is slightly noisier centroids; mitigate this with larger batch sizes, more iterations, and a held-out stability evaluation.
Deliverable-wise, k-means shines when stakeholders need crisp segment membership and you can summarize each segment with a few centroid-derived feature statements.
Choosing k is where k-means projects often go off the rails. There is no universal “correct” k; you choose a k that balances fidelity (smaller clusters fit data better) with usability (too many clusters are impossible to action). Treat k as a product decision informed by quantitative diagnostics.
The elbow method plots inertia vs. k and looks for a point where improvements diminish. In practice, elbows are often ambiguous, especially in high dimensions where inertia decreases smoothly. Use the elbow as a sanity check, not a sole decision rule. If the curve has no clear bend, that’s a signal that either (a) the data doesn’t have strong spherical cluster structure, (b) you need different features, or (c) a different algorithm fits better.
Silhouette score measures how separated clusters are by comparing each point’s within-cluster distance to its nearest other cluster. It’s intuitive: higher is better. However, silhouette tends to favor compact, well-separated clusters and may penalize valid elongated or varying-density structure. Also, computing it exactly can be expensive for large n; use sampling for practicality.
The gap statistic compares your clustering’s dispersion to what you’d expect under a reference null distribution (often uniform within the feature bounds). It’s more principled, but slower and sensitive to how you generate the reference. Use it when you need a stronger argument that “some clustering structure exists,” not when you just need a workable segmentation quickly.
Finally, validate k qualitatively: profile each cluster, name it, and ask whether a human can reliably describe why members belong together. If you can’t, you likely have either the wrong k or the wrong representation.
Gaussian Mixture Models (GMMs) extend k-means by modeling each cluster as a Gaussian distribution and assigning points probabilistically. Instead of saying “this point is in cluster 2,” you get membership probabilities across clusters. This is valuable when boundaries are inherently fuzzy—think customer segments with overlapping behavior—or when you need calibrated confidence for downstream actions.
Training uses the Expectation-Maximization (EM) algorithm: estimate responsibilities (soft assignments) given current parameters, then update means, covariances, and mixture weights. Compared to k-means, GMMs can model ellipsoidal clusters via covariance matrices, which helps when clusters are stretched or correlated across features.
The major design choice is the covariance type. A spherical covariance behaves similarly to k-means (round clusters). Diagonal allows different variances per feature but no correlations, often a good compromise for high-dimensional data. Full covariance captures correlations but can overfit and becomes expensive as dimensionality grows. A common failure mode is fitting full covariances on many features with limited data per cluster, producing unstable, nearly singular covariance estimates.
For selecting the number of components, GMMs offer criteria like BIC/AIC, which penalize complexity. These are practical when you want a model-selection story that accounts for parameter count, but still validate with stability and interpretability. Also note: a GMM assumes Gaussian-like cluster shapes; if your data has arbitrary manifolds or strong density variation, a mixture of Gaussians may “tile” the space with many components rather than revealing meaningful groups.
When you need soft segmentation or more flexible geometry than k-means (but still want a parametric, explainable model), GMMs are a strong next step.
Hierarchical clustering is your tool when you suspect nested structure: subtypes within types, or a taxonomy rather than a flat partition. It produces a tree (dendrogram) showing how clusters merge (agglomerative) or split (divisive). The practical advantage is that you can choose a “cut” level after seeing the structure, rather than committing to k upfront.
Agglomerative methods start with each point as its own cluster and repeatedly merge the closest clusters according to a linkage rule. Linkage is not a detail—it defines cluster geometry. Single linkage can chain points into long, stringy clusters and is sensitive to noise. Complete linkage prefers compact clusters but can split natural elongated groups. Average linkage is a balanced default. Ward linkage is especially popular because it merges clusters to minimize the increase in within-cluster variance (it often resembles k-means behavior but with hierarchical output).
Dendrograms are useful, but in real datasets they can become unreadable. A practical approach is to: (1) compute the hierarchy on a representative sample or on cluster prototypes, (2) inspect merge distances to find large “jumps” (candidate cut points), and (3) validate chosen cuts by profiling clusters and checking stability across samples.
The biggest constraint is complexity. Naive hierarchical clustering scales poorly with dataset size (often O(n^2) memory/time), making it unsuitable for millions of points. For large n, consider: clustering a sample, using approximate nearest neighbors, or applying hierarchical clustering to the centroids from a faster method (e.g., k-means first, then hierarchy on centroids) to reveal higher-level structure.
Use hierarchical clustering when you need interpretability of relationships between clusters and are willing to manage computational cost.
Density-based clustering is what you reach for when clusters are irregularly shaped, when you expect outliers, or when “noise” is a first-class concept. DBSCAN groups points that are in dense regions and labels sparse-region points as noise. This is a major practical difference from k-means: DBSCAN does not force every point into a cluster.
DBSCAN has two key parameters: eps (neighborhood radius) and min_samples (minimum points required to form a dense core). Points with at least min_samples neighbors within eps are core points; points reachable from cores are assigned to clusters; the rest are noise. Interpreting results means examining both cluster assignments and the fraction of noise, which can be operationally meaningful (e.g., rare behaviors, potential anomalies, or data quality issues).
Parameter tuning is practical but finicky. eps is scale-dependent: if you forget to standardize features, eps becomes meaningless. A common heuristic is a k-distance plot (distance to the kth nearest neighbor) to look for a bend that suggests a density threshold, but it’s not foolproof. min_samples is often set based on dimensionality and expected minimum cluster size; higher values make DBSCAN more conservative (more noise).
Limitations matter. DBSCAN struggles with varying density: if one cluster is dense and another is sparse, a single eps cannot capture both well. It also degrades in high dimensions where distance becomes less informative. In those cases, the “HDBSCAN-style” idea—allowing variable density and producing cluster stability scores—often works better conceptually, even if you implement it via a library choice later.
If your business problem includes anomaly detection or irregular cluster shapes, density-based methods are often the first algorithm family to try.
Choosing a clustering algorithm is easier when you treat it as a constraints problem: dataset size, feature type, geometry, and the deliverable you need to ship. Below is a practical selection matrix you can apply before running anything expensive.
Stability is the practical guardrail across all methods. For k-means/GMM, check sensitivity to random seeds and slight feature perturbations. For hierarchical, check whether the same major branches appear in bootstrap samples. For DBSCAN, test small eps/min_samples changes; if clusters flip dramatically, you may be operating at an unstable boundary or in a space where density is not well-defined.
Finally, tie algorithm choice to the action. If clusters will drive pricing, policy, or user experience, prefer methods with interpretable profiles and stable assignments. If clustering is exploratory or used as a preprocessing step, you can prioritize flexibility and shape discovery. The “right” method is the one that produces segments you can defend, monitor over time, and convert into decisions without constant re-tuning.
1. In this chapter’s framing, what is the most practical way to think about the goal of clustering in real projects?
2. Why is clustering algorithm choice described as an engineering decision as much as a statistical one?
3. Which workflow step directly addresses a common pitfall of using distance-based clustering methods on messy features?
4. You suspect your data contains irregularly shaped groups and meaningful outliers. Which approach best matches the chapter’s recommendation?
5. When using hierarchical clustering to 'choose cuts,' what output are you primarily interpreting to decide where to split the structure?
Clustering is unusual compared with supervised learning: you rarely get a single “ground-truth” answer to score against. That does not mean you can’t evaluate. It means evaluation becomes a multi-angle process: internal fit (are points close to their cluster and far from others?), stability (does the structure persist under small changes?), and usefulness (do the segments support decisions and actions?). This chapter shows a practical workflow to evaluate clusters without labels, avoid common misreads of metrics, and produce results that are reproducible and auditable.
A reliable evaluation routine typically follows this order. First, compute internal metrics to compare candidate runs and hyperparameters, but treat them as signals—not verdicts. Second, stress-test the clustering for stability across random seeds, subsamples, and time windows. Third, validate business usefulness by profiling each segment: quantify what makes it distinct and check that these differences are meaningful, not artifacts of scaling or sparsity. Finally, document every key decision so other teams can reproduce your clustering and trust it in production.
Throughout, remember that “good clustering” depends on your objective. A marketing segmentation may prefer a few interpretable groups with clear behavioral lift, while an anomaly triage system might accept many micro-clusters if they improve separation of normal vs. rare patterns. Evaluation is the bridge from algorithm output to an operational decision.
Practice note for Compute internal metrics and interpret them correctly: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Test stability across seeds, samples, and time windows: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Validate business usefulness via segment profiling: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Document decisions to make results reproducible and auditable: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Compute internal metrics and interpret them correctly: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Test stability across seeds, samples, and time windows: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Validate business usefulness via segment profiling: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Document decisions to make results reproducible and auditable: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Compute internal metrics and interpret them correctly: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Internal metrics evaluate cluster structure using only the data and assignments. They help you compare runs (e.g., different k for k-means, linkage choices for hierarchical clustering, or eps/min_samples for DBSCAN) when you have no labels. The most common metrics are silhouette, Davies–Bouldin (DB), and Calinski–Harabasz (CH). Use them to rank candidates, then inspect the top few with profiling and stability checks.
Silhouette measures how much closer a point is to its own cluster than to the nearest other cluster. It ranges from -1 to 1; higher is better. Engineering judgment: compute the average silhouette, but also examine the distribution by cluster. A single tiny, very tight cluster can inflate the average while most points are ambiguous. Another common mistake is computing silhouette on a distance metric that does not match the model (e.g., Euclidean silhouette for cosine-based text embeddings); align the metric to your representation and clustering method.
Davies–Bouldin summarizes cluster compactness vs. separation; lower is better. It is sensitive to clusters of very different sizes and can be overly optimistic when the model creates many small clusters. Use DB to detect obvious over-fragmentation: if DB improves steadily as you increase k, you may be splitting noise rather than uncovering new structure.
Calinski–Harabasz is the ratio of between-cluster dispersion to within-cluster dispersion; higher is better. CH often favors solutions with more clusters, especially in high dimensions. Treat it as a “does separation exist?” indicator, not a precise selector of k. In sparse or high-dimensional settings, internal metrics can be distorted by the curse of dimensionality; if distances become uniform, silhouette and CH can flatten, and DB can behave erratically.
Practical outcome: internal metrics narrow the search, but your final choice should survive stability testing and produce segments you can explain and act on.
Sometimes you do have labels—just not the labels you wish you had. Proxy evaluation uses partial, noisy, or downstream signals to validate whether clusters align with something meaningful. Examples include churn (available weeks later), fraud chargebacks (rare and delayed), support tickets, product tier, geography, or manually reviewed samples. The idea is not to “turn clustering into classification,” but to check whether clusters correlate with relevant outcomes more than you would expect by chance.
A practical approach is to compute cluster-outcome lift. For each cluster, compare the outcome rate to the overall baseline. If Cluster 3 has a 12% churn rate vs. a 5% baseline, that is 2.4× lift—useful for targeting retention efforts. For continuous outcomes (e.g., revenue), compare means/medians and use robust statistics (median and IQR) when distributions are skewed. Where sample sizes are small, attach uncertainty: confidence intervals or bootstrap intervals prevent overreacting to noise.
Be cautious about leakage and tautologies. If one of your features is “number of support tickets,” and your proxy label is also derived from support activity, your clusters may appear predictive while merely restating the same signal. Similarly, if time is involved, validate on a time-split: build clusters on a historical window and measure proxy outcomes in a later window to mimic real deployment.
Practical outcome: proxy evaluation helps you argue that segments are not arbitrary geometry—they relate to business or operational signals in a measurable way.
Two clusterings can score similarly on internal metrics but behave very differently when the data shifts slightly. Stability analysis asks: if you rerun the pipeline with small changes, do you get essentially the same partition? This is critical for reproducibility, auditing, and for preventing “segments” that disappear next week.
Across seeds: algorithms like k-means are sensitive to initialization. Run multiple seeds and compare assignments using a label-invariant similarity measure such as Adjusted Rand Index (ARI) or Normalized Mutual Information (NMI). If ARI varies wildly, you likely have weak structure, poor scaling, or an ill-chosen k. Record the chosen seed or use a deterministic initialization policy if governance requires it.
Subsampling and bootstraps: repeatedly cluster on random subsets (e.g., 70–90% of points). Then map clusters back to the full set (or compare only within the overlap) and quantify consistency. For large datasets, subsampling also reveals whether the algorithm is latching onto outliers. If a cluster only appears in certain subsamples, it may be a fragile artifact rather than a stable segment.
Perturbations: introduce controlled noise—small feature jitter, alternative scaling choices, or slight variations in encoding (e.g., different hashing seeds). This tests robustness to preprocessing, which is often the true source of instability. For time-evolving systems, do a time window stability check: cluster on one month, then re-run on the next month and measure drift in cluster profiles and membership.
Practical outcome: stability testing turns clustering from a one-off exploration into an engineering artifact you can trust under routine data variation.
Profiling is where clusters become segments. The goal is to describe each cluster in plain language supported by numbers: what is typical here, what is unusually high/low, and how confident are we? Start with basic summary stats per cluster: size, key numeric feature medians, and categorical distributions. Then identify the “top features” that differentiate clusters using standardized differences or simple models (e.g., one-vs-rest logistic regression with strong regularization) to highlight separating signals.
A particularly practical tool is lift/enrichment. For a binary attribute (e.g., “uses feature X”), compute the cluster rate divided by the overall rate. For example, if 40% of Cluster A uses feature X vs. 10% overall, enrichment is 4×. For categorical attributes, compare each category’s share within the cluster to its global share. For numeric features, report effect sizes (difference in medians divided by overall IQR) to avoid being misled by large scales.
Engineering judgment matters in choosing which features to profile. If your input space is hundreds of sparse indicators, raw averages can be unreadable. Prefer: (1) a curated set of business features for interpretation, even if the model uses many more; and (2) grouped features (e.g., “engagement last 7 days” rather than 30 separate event counts). Also, watch for confounders: a “high-value” cluster might simply be “enterprise customers” if plan tier is included. That can still be valid—just be explicit about it.
Practical outcome: profiling validates business usefulness by turning geometry into narratives stakeholders can test, critique, and operationalize.
Visualization is not a substitute for metrics, but it is a powerful debugging tool and a communication aid. The trick is to choose visuals that match your data type and avoid misleading “pretty plots.” Start simple: for a small set of interpretable numeric features, use pair plots (scatterplot matrix) colored by cluster to see separation and overlap. Add density contours or transparency for large datasets to avoid overplotting.
For high-dimensional data, use embeddings such as PCA (linear, fast, often a good first look) and then UMAP or t-SNE (nonlinear) for local structure. A common mistake is to interpret UMAP/t-SNE distances as literal separation: these methods distort global geometry. Use them to ask, “Are clusters intermingled?” and “Do we see sub-structure?”, not to prove optimality. When possible, annotate plots with cluster sizes and silhouette-by-cluster so viewers understand which groups are solid vs. ambiguous.
To make clusters tangible, show exemplars. For k-means, display centroids in the original feature units (after inverting scaling) for a small set of key features. For arbitrary distance metrics or non-spherical clusters, use medoids: actual data points closest to the cluster center under your distance function. In text or product data, exemplars can be sample documents, representative sessions, or archetypal baskets. Stakeholders often gain more trust from three well-chosen exemplars than from a single metric value.
Practical outcome: visual checks reveal preprocessing bugs, boundary ambiguity, and whether segments are interpretable enough to use.
Unsupervised models still need documentation. In production, clusters become part of decisions: eligibility rules, routing, targeting, or monitoring. A lightweight “model card” for clustering makes results reproducible and auditable, and it prevents silent drift when data or code changes.
Your report should capture four categories of decisions. Objective and scope: what business question the clustering serves, what entities are clustered (users, transactions), and what the clusters will be used for (and not used for). Data and features: time range, sampling, missingness handling, scaling/encoding, and any feature exclusions for policy or leakage reasons. Model and selection: algorithm, hyperparameters, distance metric, candidate comparison table (silhouette/DB/CH), and the rationale for the final choice. Validation and monitoring: stability results (seed/subsample/time), profiling summaries, proxy outcomes (if any), and a plan to detect drift (e.g., changes in cluster sizes, centroid movement, or enrichment shifts).
Practical outcome: a strong cluster report turns an exploratory notebook into an operational artifact—repeatable by another engineer, explainable to stakeholders, and defensible in audits.
1. Why does cluster evaluation in this chapter require a “multi-angle process” rather than a single score?
2. What is the recommended order of a reliable evaluation routine for clustering without labels?
3. How should internal clustering metrics be interpreted when comparing candidate runs or hyperparameters?
4. Which approach best matches the chapter’s idea of testing clustering stability?
5. What is the primary purpose of segment profiling in evaluating clusters without labels?
Anomaly detection is where unsupervised learning becomes operational: you are not just “finding structure,” you are deciding when to interrupt a process, open an investigation, or block an action. That means you must connect modeling choices to alerting policies, triage capacity, and the real-world cost of misses versus false alarms. In practice, most projects fail not because the model is weak, but because thresholds are arbitrary, data leakage sneaks in, or the team cannot evaluate quality with limited labels.
This chapter treats anomaly detection as an end-to-end workflow. You will define what “anomalous” means for your business problem, build simple baselines that are hard to beat, then add learned methods such as Isolation Forest and density-based scoring. Throughout, you will tune with engineering judgment: choosing features and scaling, selecting score calibration strategies, and designing evaluation when ground truth is incomplete. The goal is a detector that produces actionable alerts—stable, explainable enough for operators, and aligned with your constraints.
A useful mental model is: (1) define the anomaly type and unit of analysis, (2) choose a scoring method, (3) choose a thresholding and alerting policy, (4) validate with whatever labels or proxies you have, (5) monitor drift and recalibrate. The sections below give concrete tools for each step, along with common mistakes and practical outcomes.
Practice note for Define anomalies, thresholds, and alerting policies: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Build baseline detectors and compare against learned methods: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Train and tune Isolation Forest and density-based detectors: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Evaluate anomalies with limited labels and operational constraints: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Define anomalies, thresholds, and alerting policies: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Build baseline detectors and compare against learned methods: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Train and tune Isolation Forest and density-based detectors: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Evaluate anomalies with limited labels and operational constraints: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Define anomalies, thresholds, and alerting policies: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Start by defining “anomaly” in terms your stakeholders can sign off on. An anomaly is not a property of the data alone; it is a deviation that matters for a decision. Write down the unit of detection (transaction, device-day, user-session, batch job run) and the action (alert, block, route to review, log only). This prevents the common mistake of scoring at the wrong granularity—e.g., flagging individual events when the real risk emerges only as a pattern over a week.
There are three practical anomaly types. A point anomaly is a single observation that looks unusual given the overall data distribution (e.g., a payment amount far above normal). A contextual anomaly is only anomalous under a specific context such as time, location, segment, or operating mode (e.g., high traffic at 3am is unusual, but high traffic at noon is normal). A collective anomaly is a set of observations that together form an unusual pattern even if each point looks normal (e.g., many small transfers to new recipients, or a gradual sensor drift that stays within per-reading bounds).
Defining the type guides feature engineering and evaluation. Point anomalies often work with global scaling and a single score threshold. Contextual anomalies require conditioning (seasonality, device class, customer tier) so the model learns “normal for that context.” Collective anomalies require windowing or sequence features; if you only score single events, you will miss the pattern.
Finally, specify your alerting policy early: do you want a fixed daily alert volume, a risk-based threshold, or a “top-k” triage list? These choices affect how you set thresholds and how you evaluate success when labels are sparse.
Baseline detectors are essential because they are fast, interpretable, and often competitive. Build them first and use them as a yardstick for learned models. A good baseline also exposes data issues: missing values, heavy tails, and non-stationarity will show up immediately in unstable thresholds.
The simplest baseline is a z-score: score = (x − mean) / std. It works well when a feature is roughly Gaussian and stable. In practice, z-scores break under outliers (they inflate std) and under drift (mean shifts). Prefer to compute z-scores within a relevant context (per device model, per store, per hour-of-day) and to re-estimate parameters on a rolling window when the process changes.
A more robust alternative is MAD (median absolute deviation): score = (x − median) / (1.4826 × MAD). MAD handles heavy-tailed distributions and single spikes better than std. It is a practical default for numeric telemetry, latency, and counts. Common engineering mistake: computing MAD on a window that includes the anomaly period you are trying to detect, which reduces sensitivity. Use past-only windows for online systems.
When anomalies are multivariate (the combination is strange even if each feature is fine), use robust covariance ideas. The classical tool is Mahalanobis distance, but with robust estimates of center and covariance to reduce outlier influence (e.g., Minimum Covariance Determinant or shrinkage-based robust estimators). This detects “unlikely combinations,” such as a user who logs in from a typical country and a typical device—but not in that pairing. Practical note: robust covariance is sensitive to scaling and collinearity; standardize features and remove near-duplicates. Always compare multivariate baselines against univariate rules to ensure the complexity is justified.
Isolation Forest is a strong general-purpose anomaly detector for tabular data because it does not assume a particular distribution. The intuition is simple: anomalies are easier to “isolate” with random splits. The algorithm builds many random trees; points that end up with short average path lengths are considered anomalous. This tends to work well when anomalies are sparse and differ in feature values from normal data.
Key parameters control stability and operational behavior. n_estimators (number of trees) increases score stability; more trees reduce variance but cost more compute. max_samples controls subsampling; smaller subsamples can help isolation but may miss rare normal patterns. max_features (feature subsampling) can improve robustness when many features are noisy. bootstrap can help on small datasets but may reduce diversity.
The most operationally important setting is contamination, which represents the expected fraction of anomalies and is used to map scores into a decision threshold. Treat contamination as a policy knob, not a “truth.” If your team can only review 200 cases/day, contamination should be calibrated to deliver that volume given current traffic. If you do have partial labels, tune contamination to hit a target precision or acceptable false-positive rate for a subset.
Common mistakes include: (1) feeding unscaled numeric features with wildly different ranges, causing splits to be dominated by large-magnitude features; (2) including identifiers with high cardinality (user_id as numeric) which creates meaningless separations; and (3) training on data that already contains an incident spike, making the model normalize the very behavior you want to catch. A practical workflow is: start with a baseline, train Isolation Forest on a “clean” time range, inspect top anomalies for face validity, then iterate on features and contamination until alert volumes and investigation outcomes are acceptable.
Density-based detectors flag points that sit in sparse regions relative to their neighbors. They are useful when “normal” is multi-modal (several clusters of normal behavior) and you want anomalies that fall outside these regions. Two practical tools are Local Outlier Factor (LOF) and k-nearest-neighbor (kNN) distance scoring.
kNN distance scoring is straightforward: compute the distance to the k-th nearest neighbor (or average distance to k neighbors). Larger distances imply more isolation. This method is easy to explain and can work surprisingly well with good feature scaling. It is sensitive to the curse of dimensionality: in high dimensions, distances become less informative. Practical mitigations include reducing dimensionality (PCA on numeric features), using domain-driven feature selection, and using cosine distance for sparse vectors (e.g., text or high-dimensional categorical encodings).
LOF goes further by comparing a point’s local density to the density of its neighbors. This helps detect anomalies in regions of varying density—e.g., a point may be far from the global mean but still inside a legitimate sparse cluster; LOF is less likely to flag it if its neighbors are similarly sparse. LOF’s key parameter is n_neighbors: too small makes scores noisy; too large makes LOF behave like a global method. Start with 20–50 for moderate datasets, then tune for stability of the top-k list across weeks or across bootstrap samples.
Operationally, density methods are often heavier than Isolation Forest at inference because they require neighbor searches. For production, consider approximate nearest neighbor indexes or precomputing embeddings and scoring in batches. A frequent mistake is evaluating LOF on the same dataset used to fit neighbors without thinking about time: if you fit on “today,” anomalies can become each other’s neighbors and look normal. Fit on historical normal windows and score forward in time when the use case is monitoring.
Many real anomaly problems are time-aware even if the model is not explicitly temporal. The moment you alert on metrics over time, you must handle windows, seasonality, and data leakage. Start by choosing the window that matches the action: per minute for outages, per hour for abuse spikes, per day for accounting anomalies. For collective anomalies, construct features like rolling sums, rolling unique counts, change rates, and “time since last event.”
Seasonality is the most common reason for false alerts. Daily and weekly cycles can produce predictable spikes. Practical strategies include: (1) create seasonal baselines (separate distributions for each hour-of-week), (2) include time context features (hour, day-of-week) and let the model learn conditional normals, or (3) detrend with a simple forecasting model and run anomaly detection on residuals. Keep the approach as simple as your failure mode: if hourly seasonality explains 80% of false positives, fix that before adding complex detectors.
Leakage traps are subtle in unsupervised settings. Leakage occurs when features include information from the future relative to the detection time, or when your training window includes the incident period. Examples: using “daily total” to detect anomalies at noon (it contains future transactions), or computing normalization statistics over a full month that includes a fraud campaign. The remedy is discipline: use past-only windows, compute scaling parameters on training data only, and adopt a backtesting setup where you repeatedly train on a historical span and score the next span.
Finally, decide whether thresholds should be static or adaptive. In systems with drift, a static threshold creates alert floods or blind spots. Adaptive thresholds—based on rolling quantiles of scores or on a fixed daily alert budget—often align better with operational constraints, but they require careful monitoring so “normalization” does not hide genuine step-changes.
Anomaly detection is usually evaluated with limited labels: you might have a handful of confirmed incidents, partial investigation outcomes, or delayed ground truth. Instead of forcing a single accuracy number, evaluate in a way that matches how the system will be used: ranking quality, alert volume control, and cost trade-offs.
When your workflow is a review team looking at the top alerts, use precision@k: among the top k highest-scoring alerts, how many are true issues? Choose k to match daily or weekly triage capacity. Track precision@k over time and across segments (regions, device types) to ensure the detector is not only good on average. If labels are sparse, use proxy labels such as “investigation opened,” “chargeback occurred,” or “ticket severity,” but document the bias these introduce.
Translate scores into an alerting policy. Common policies include: (1) fixed threshold on score, (2) fixed percentile (e.g., top 0.1% per day), and (3) fixed quota (top N per hour). Percentile and quota policies stabilize alert volume and are often easier to operate, but they can miss periods where anomalies truly increase; mitigate by adding a secondary “absolute” threshold that triggers when scores exceed historical extremes.
Use triage queue thinking: alerts should contain context (top contributing features, recent history, comparable peers) so reviewers can decide quickly. Even if the model is unsupervised, you can attach explanations: for baselines, show the deviation and reference distribution; for Isolation Forest, provide feature-wise comparisons to medians; for kNN/LOF, show nearest neighbors and distances.
Finally, make costs explicit with cost curves. Estimate the cost of a false positive (review time, customer friction) and a false negative (loss, downtime). Sweep thresholds and plot expected total cost. This turns thresholding from an argument into a decision. In production, re-evaluate thresholds after major product changes, traffic shifts, or feature pipeline updates, and monitor score distributions for drift to avoid silent failure.
1. Why do anomaly detection projects often fail in practice even when a model seems reasonable?
2. Which consideration best connects anomaly detection to real-world operations?
3. What is the purpose of building simple baseline detectors before trained methods like Isolation Forest?
4. Which sequence best matches the chapter’s end-to-end anomaly detection workflow mental model?
5. When ground-truth labels for anomalies are incomplete, what does the chapter recommend for evaluation and tuning?
Clustering is only “done” when someone can make a decision with it. In earlier chapters you built models, tuned hyperparameters, checked internal metrics, and validated stability. This chapter focuses on delivery: turning clusters into segments with names, rules, and narratives; embedding segmentation into products and analytics; monitoring drift and retraining safely; and shipping an end-to-end blueprint that combines clustering with anomaly monitoring.
A useful mindset is to treat clustering outputs as a hypothesis generator, not a final truth. The model suggests groupings in the feature space; your job is to translate those groupings into a segmentation that is measurable, stable enough to operationalize, and aligned to an intervention (personalization, pricing, outreach, risk review, and so on). You will often create a thin “semantic layer” on top of the raw cluster labels: profiling, naming, and simple rules that let business users understand and act.
Finally, delivery requires engineering judgment. A segmentation that looks great in a notebook can fail in production because feature definitions drift, new categories appear, batch pipelines lag, or the organization cannot agree on segment ownership. You will learn pragmatic patterns for deployment, monitoring, and governance so segments stay trustworthy and safe.
The sections below walk through a concrete workflow from raw clusters to decisions, with common mistakes and how to avoid them.
Practice note for Turn clusters into named segments with rules and narratives: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Operationalize segmentation in products and analytics: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Monitor drift and trigger retraining safely: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Ship a capstone blueprint: clustering + anomaly monitoring pipeline: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Turn clusters into named segments with rules and narratives: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Operationalize segmentation in products and analytics: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Monitor drift and trigger retraining safely: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Ship a capstone blueprint: clustering + anomaly monitoring pipeline: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Practice note for Turn clusters into named segments with rules and narratives: document your objective, define a measurable success check, and run a small experiment before scaling. Capture what changed, why it changed, and what you would test next. This discipline improves reliability and makes your learning transferable to future projects.
Raw cluster IDs (0, 1, 2, 3…) are not segments. A segment is a decision unit: a group you can describe, measure over time, and target with a consistent action. Start with profiling: compute per-cluster summaries for each key feature (means/medians, category shares), plus business KPIs that were not used for clustering (conversion, retention, margin, support tickets). This separates “shape in feature space” from “meaning in outcomes.”
Next, turn profiles into narratives and rules. Narratives are human-readable descriptions (“Price-sensitive occasional buyers”) grounded in the statistics. Rules are minimal, stable heuristics that approximate the cluster (e.g., “visits/month < 2 and discount_share > 0.6”), used for communication and as guardrails. You should not replace the model with rules unless you have to; instead, use rules to explain and sanity-check.
Common mistakes include designing segments that are descriptive but not actionable (“Users with medium activity”), using unstable features (session-level randomness) for assignment, and overfitting the narrative to one time period. A practical stability check is to score consecutive time windows and compute a transition matrix: if 30–50% of users switch segments week-to-week without a product change, the segmentation is likely too sensitive (or your features are). Consider smoothing features (rolling windows), reducing dimensionality, or choosing a more robust clustering approach.
End this step with a segment dictionary: name, definition, top differentiators, typical behaviors, anti-examples, and recommended actions. This document becomes the contract between data science, analytics, and product teams.
Segmentation is valuable when it changes what you do. For each segment, define an intervention hypothesis, an expected outcome, and a measurement plan. A tight template is: “For segment S, do X, because trait T suggests mechanism M; success is metric Y over window W.” This forces clarity and avoids “segment tourism,” where teams admire clusters but never act.
Personalization examples: change onboarding flows for “new but highly engaged” users; adjust recommendations for “broad explorers” versus “single-category loyalists”; vary notification cadence for “habitual daily users” versus “fragile returners.” Pricing examples: offer bundles to “high frequency, low basket size” customers; reduce discounts for “high willingness-to-pay” segments (carefully, with governance); increase trials for “curious but hesitant” segments. Outreach examples: route “at-risk high value” accounts to human success teams; send self-serve education to “confused first-timers” identified by error events and low task completion.
A frequent mistake is optimizing interventions using the same features that defined the clusters, then declaring success. Instead, evaluate on downstream metrics (retention, margin, NPS) and include holdout periods. Another mistake is creating too many segments. If teams cannot remember or operationalize them, consolidate: it is often better to have 4–8 strong segments than 15 weak ones.
Finally, define escalation paths for anomalies: if anomaly monitoring flags a spike in rare behavior within a segment, decide whether the response is product debugging, fraud review, or a temporary pause of automated interventions.
Operationalizing segmentation means producing segment labels (and optional anomaly scores) reliably, at the latency your use case requires. Most segmentation starts with batch scoring: nightly or weekly jobs compute features (rolling aggregates), apply the preprocessing pipeline (scaling/encoding), then assign clusters and write results to a table consumed by analytics and campaigns.
Batch is robust and easier to govern, but not always sufficient. If you need in-session personalization or fraud-like anomaly detection, you may need streaming or near-real-time scoring. In that case, keep the clustering model lightweight and ensure the feature computation is available online. This is where feature stores help: they standardize feature definitions and keep offline and online values consistent.
Engineering judgment: keep the preprocessing steps versioned and bundled with the model (a single pipeline artifact). Many production failures come from training with one scaler/encoder and serving with another. Also, handle missingness and unseen categories intentionally: define defaults, “other” buckets, and minimum data requirements before assigning a segment (“insufficient history” can be its own operational segment).
For analytics, store both the hard label and soft diagnostics: distance-to-centroid (k-means), membership probability (if available), and a stability/confidence flag. These are invaluable for debugging and for safe use in downstream decisions (e.g., only apply pricing intervention when confidence is high).
Segments decay. User behavior changes, products ship new flows, marketing alters acquisition mix, and data pipelines evolve. You need monitoring at three layers: feature drift, cluster drift, and decision drift (impact).
Feature drift checks compare current feature distributions to a reference window (training period or last stable month). Practical metrics include population stability index (PSI) for binned numeric features, KL divergence for categorical distributions, and simple percentile shifts for heavy-tailed variables. Alert when multiple key features drift, not just one.
Cluster drift checks track whether the segmentation still “fits.” For centroid-based models, monitor centroid movement and average distance-to-centroid per segment; rising distances suggest the model no longer represents the population. For density-based approaches, monitor the share of points labeled as noise/outliers and changes in local density. Also track the segment size distribution: sudden changes can indicate data issues or real market changes.
Retraining should be triggered safely. Define thresholds (e.g., PSI > 0.2 on 3+ key features, or average distance-to-centroid up 25% for two consecutive weeks) and include a human review step. When retraining, ensure segment continuity: stakeholders hate when “Segment B” changes meaning overnight. Techniques include aligning new clusters to old ones via centroid matching, reusing initialization from prior centroids, or publishing a new segmentation version with a migration plan.
A common mistake is retraining automatically without validating downstream impact. Your monitoring should include decision metrics: did interventions stop working? If the segment-targeted campaign lift collapses, it may be model drift, but it could also be market saturation or creative fatigue. Treat drift alerts as investigation starters, not automatic truth.
Segmentation can create sensitive inferences even if you never use explicitly sensitive features. Governance is the set of practices that make segmentation safe, lawful, and trusted. Start with privacy: document data sources, retention periods, and whether features could reveal sensitive attributes (health status, children, financial hardship). Apply data minimization: only use features necessary for the segmentation objective, and aggregate where possible.
Fairness checks matter because segments often drive differential treatment (offers, service levels, pricing). Evaluate disparate impact across protected or policy-relevant groups where legally and ethically appropriate. Even in unsupervised settings, you can measure whether protected groups are overrepresented in segments that receive negative interventions (e.g., reduced access, higher scrutiny). If you cannot use protected attributes, use proxy and geographic risk assessments and focus on outcome parity and complaint monitoring.
Common mistakes: letting marketing rename segments in ways that imply protected traits (“low income”) without evidence or permission; using anomaly scores as “fraud labels” without validation; and failing to document changes. Treat segment names as part of governance: they shape how teams think and act. Prefer neutral, behavior-based names tied to observable signals.
Close governance with a cadence: quarterly reviews of segment performance and drift, plus an approval process for new interventions that use segmentation. This keeps the system aligned with evolving policies and business goals.
This capstone blueprint combines clustering and anomaly monitoring into a production-ready pipeline. The goal is not just to compute clusters, but to hand off a maintainable segmentation product.
Handoff checklist (what must be true before you “ship”): (1) segment dictionary approved; (2) reproducible scoring with pinned feature definitions; (3) logging of assignments with versions; (4) monitoring dashboards live with alert thresholds; (5) governance sign-off for privacy and fairness risks; (6) documented playbooks for drift alerts and anomaly spikes; (7) clear ownership—who maintains features, model, and interventions.
If you complete this checklist, your segmentation moves from a clustering exercise to a decision system: explainable segments, operational pipelines, and safe monitoring that keeps the model useful as reality changes.
1. According to the chapter, when is clustering considered “done”?
2. What is the recommended mindset for interpreting clustering outputs during delivery?
3. What is the purpose of creating a “thin semantic layer” over raw cluster labels?
4. Which production issue is highlighted as a reason a segmentation can fail even if it looks good in a notebook?
5. Which set of deliverables best matches the chapter’s end-to-end segmentation delivery blueprint?